您好,登錄后才能下訂單哦!
您好,登錄后才能下訂單哦!
本篇內容主要講解“LyScript怎么實現Hook隱藏調試器”,感興趣的朋友不妨來看看。本文介紹的方法操作簡單快捷,實用性強。下面就讓小編來帶大家學習“LyScript怎么實現Hook隱藏調試器”吧!
我們以此實現Patches如下函數:
IsDebuggerPresent
ZwQueryInformationProcess
CheckRemoteDebuggerPresent
PEB.IsDebugged
PEB.ProcessHeap.Flag
PEB.NtGlobalFlag
PEB.Ldr 0xFEEEFEEE filling
GetTickCount
ZwQuerySystemInformation
FindWindowA
FindWindowW
FindWindowExA
FindWindowExW
EnumWindows
首先第一步我們需要自己封裝實現一個反匯編轉機器碼的函數,其作用是當用戶傳入匯編列表時,自動將其轉為機器碼并輸出為列表格式。
from LyScript32 import MyDebug
# 傳入匯編代碼,得到對應機器碼
def get_opcode_from_assemble(dbg_ptr,asm):
byte_code = bytearray()
addr = dbg_ptr.create_alloc(1024)
if addr != 0:
asm_size = dbg_ptr.assemble_code_size(asm)
# print("匯編代碼占用字節: {}".format(asm_size))
write = dbg_ptr.assemble_write_memory(addr,asm)
if write == True:
for index in range(0,asm_size):
read = dbg_ptr.read_memory_byte(addr + index)
# print("{:02x} ".format(read),end="")
byte_code.append(read)
dbg_ptr.delete_alloc(addr)
return byte_code
else:
return bytearray(0)
# 傳入匯編機器碼得到機器碼列表
def GetOpCode(dbg, Code):
ShellCode = []
for index in Code:
ref = get_opcode_from_assemble(dbg,index)
for opcode in ref:
ShellCode.append(opcode)
return ShellCode
if __name__ == "__main__":
dbg = MyDebug()
connect = dbg.connect()
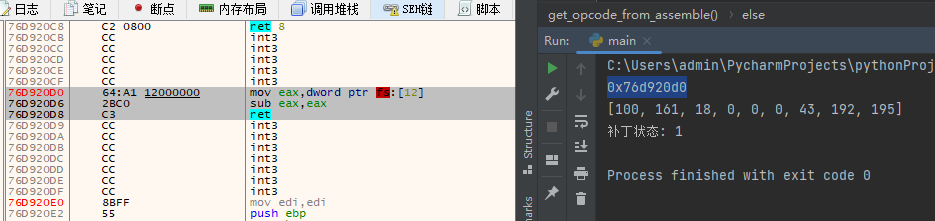
ShellCode = GetOpCode(dbg, ["DB 0x64","mov eax,dword ptr ds:[18]","sub eax,eax","ret"])
print(ShellCode)
dbg.close()輸出效果如下:

PEB結構存在許多反調試變量,首先我們需要先將這些變量填充為空。
# ----------------------------------------------
# By: LyShark
# Email: me@lyshark.com
# Project: https://github.com/lyshark/LyScript
# ----------------------------------------------
from LyScript32 import MyDebug
# 傳入匯編代碼,得到對應機器碼
def get_opcode_from_assemble(dbg_ptr,asm):
byte_code = bytearray()
addr = dbg_ptr.create_alloc(1024)
if addr != 0:
asm_size = dbg_ptr.assemble_code_size(asm)
# print("匯編代碼占用字節: {}".format(asm_size))
write = dbg_ptr.assemble_write_memory(addr,asm)
if write == True:
for index in range(0,asm_size):
read = dbg_ptr.read_memory_byte(addr + index)
# print("{:02x} ".format(read),end="")
byte_code.append(read)
dbg_ptr.delete_alloc(addr)
return byte_code
else:
return bytearray(0)
# 傳入匯編機器碼得到機器碼列表
def GetOpCode(dbg, Code):
ShellCode = []
for index in Code:
ref = get_opcode_from_assemble(dbg,index)
for opcode in ref:
ShellCode.append(opcode)
return ShellCode
def Patch_PEB(dbg):
PEB = dbg.get_peb_address(dbg.get_process_id())
if PEB == 0:
return 0
# 寫出0 Patching PEB.IsDebugged
dbg.write_memory_byte(PEB + 0x2,GetOpCode(dbg,["db 0"])[0])
print("補丁地址: {}".format(hex(PEB+0x2)))
# 寫出0 Patching PEB.ProcessHeap.Flag
temp = dbg.read_memory_dword(PEB + 0x18)
temp += 0x10
dbg.write_memory_dword(temp, GetOpCode(dbg,["db 0"])[0])
print(("補丁地址: {}".format(hex(temp))))
# 寫出0 atching PEB.NtGlobalFlag
dbg.write_memory_dword(PEB+0x68, 0)
print(("補丁地址: {}".format(hex(PEB+0x68))))
# 循環替換 Patch PEB_LDR_DATA 0xFEEEFEEE fill bytes about 3000 of them
addr = dbg.read_memory_dword(PEB + 0x0c)
while addr != 0:
addr += 1
try:
b = dbg.read_memory_dword(addr)
c = dbg.read_memory_dword(addr + 4)
# 僅修補填充運行
print(b)
if (b == 0xFEEEFEEE) and (c == 0xFEEEFEEE):
dbg.write_memory_dword(addr,0)
dbg.write_memory_dword(addr + 4, 0)
print("patch")
except Exception:
break
if __name__ == "__main__":
dbg = MyDebug()
connect = dbg.connect()
Patch_PEB(dbg)
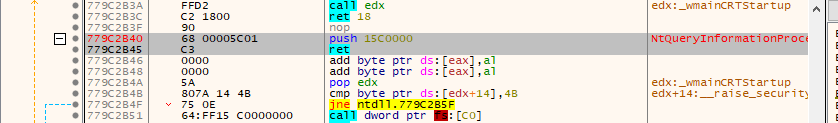
dbg.close()該函數用于檢測自身是否處于調試狀態,其C系列代碼如下所示,繞過此種方式很簡單,只需要在函數頭部寫出ret指令即可。
#include <Windows.h>
#include <stdio.h>
int _tmain(int argc, _TCHAR* argv[])
{
BOOL ref = IsDebuggerPresent();
printf("是否被調試: %d \n", ref);
getchar();
return 0;
}注意:此Api檢查PEB中的值,因此如果修補PEB,則無需修補Api,這段繞過代碼如下。
from LyScript32 import MyDebug
# 傳入匯編代碼,得到對應機器碼
def get_opcode_from_assemble(dbg_ptr,asm):
byte_code = bytearray()
addr = dbg_ptr.create_alloc(1024)
if addr != 0:
asm_size = dbg_ptr.assemble_code_size(asm)
# print("匯編代碼占用字節: {}".format(asm_size))
write = dbg_ptr.assemble_write_memory(addr,asm)
if write == True:
for index in range(0,asm_size):
read = dbg_ptr.read_memory_byte(addr + index)
# print("{:02x} ".format(read),end="")
byte_code.append(read)
dbg_ptr.delete_alloc(addr)
return byte_code
else:
return bytearray(0)
# 傳入匯編機器碼得到機器碼列表
def GetOpCode(dbg, Code):
ShellCode = []
for index in Code:
ref = get_opcode_from_assemble(dbg,index)
for opcode in ref:
ShellCode.append(opcode)
return ShellCode
def Patch_IsDebuggerPresent(dbg):
# 得到模塊句柄
ispresent = dbg.get_module_from_function("kernel32.dll","IsDebuggerPresent")
print(hex(ispresent))
if(ispresent <= 0):
print("無法得到模塊基地址,請以管理員方式運行調試器.")
return 0
# 將反調試語句轉為機器碼
ShellCode = GetOpCode(dbg, ["DB 0x64", "mov eax,dword ptr ds:[18]", "sub eax,eax", "ret"])
print(ShellCode)
flag = 0
for index in range(0,len(ShellCode)):
flag = dbg.write_memory_byte(ispresent + index,ShellCode[index])
if flag:
flag = 1
else:
flag = 0
return flag
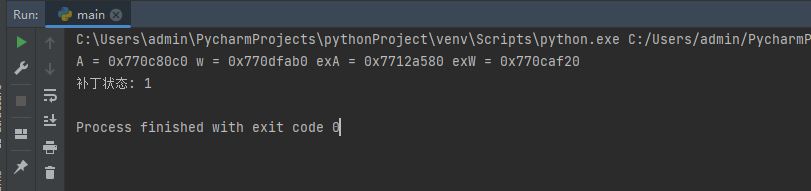
if __name__ == "__main__":
dbg = MyDebug()
connect = dbg.connect()
ref = Patch_IsDebuggerPresent(dbg)
print("補丁狀態: {}".format(ref))
dbg.close()當程序運行后會向IsDebuggerPresent函數寫出返回,從而實現繞過調試的目的。
此Api調用ZwQueryInformationProcess因此通常不需要對兩者進行修補。
from LyScript32 import MyDebug
# 傳入匯編代碼,得到對應機器碼
def get_opcode_from_assemble(dbg_ptr,asm):
byte_code = bytearray()
addr = dbg_ptr.create_alloc(1024)
if addr != 0:
asm_size = dbg_ptr.assemble_code_size(asm)
# print("匯編代碼占用字節: {}".format(asm_size))
write = dbg_ptr.assemble_write_memory(addr,asm)
if write == True:
for index in range(0,asm_size):
read = dbg_ptr.read_memory_byte(addr + index)
# print("{:02x} ".format(read),end="")
byte_code.append(read)
dbg_ptr.delete_alloc(addr)
return byte_code
else:
return bytearray(0)
# 傳入匯編機器碼得到機器碼列表
def GetOpCode(dbg, Code):
ShellCode = []
for index in Code:
ref = get_opcode_from_assemble(dbg,index)
for opcode in ref:
ShellCode.append(opcode)
return ShellCode
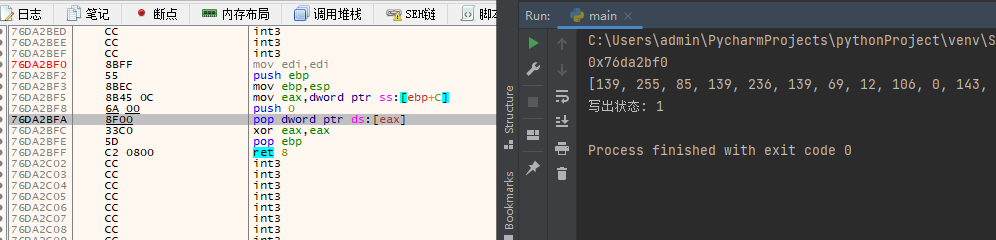
def Patch_CheckRemoteDebuggerPresent(dbg):
# 得到模塊句柄
ispresent = dbg.get_module_from_function("kernel32.dll","CheckRemoteDebuggerPresent")
print(hex(ispresent))
# 將反調試語句轉為機器碼
ShellCode = GetOpCode(dbg,
[
"mov edi,edi",
"push ebp",
"mov ebp,esp",
"mov eax,[ebp+0xc]",
"push 0",
"pop dword ptr ds:[eax]",
"xor eax,eax",
"pop ebp",
"ret 8"
]
)
print(ShellCode)
flag = 0
for index in range(0,len(ShellCode)):
flag = dbg.write_memory_byte(ispresent + index,ShellCode[index])
if flag:
flag = 1
else:
flag = 0
return flag
if __name__ == "__main__":
dbg = MyDebug()
connect = dbg.connect()
ref = Patch_CheckRemoteDebuggerPresent(dbg)
print("寫出狀態: {}".format(ref))
dbg.close()寫出效果如下:
GetTickCount返回(retrieve)從操作系統啟動所經過(elapsed)的毫秒數,常用于定時計數,繞過方式只需初始化即可。
from LyScript32 import MyDebug
# 傳入匯編代碼,得到對應機器碼
def get_opcode_from_assemble(dbg_ptr,asm):
byte_code = bytearray()
addr = dbg_ptr.create_alloc(1024)
if addr != 0:
asm_size = dbg_ptr.assemble_code_size(asm)
# print("匯編代碼占用字節: {}".format(asm_size))
write = dbg_ptr.assemble_write_memory(addr,asm)
if write == True:
for index in range(0,asm_size):
read = dbg_ptr.read_memory_byte(addr + index)
# print("{:02x} ".format(read),end="")
byte_code.append(read)
dbg_ptr.delete_alloc(addr)
return byte_code
else:
return bytearray(0)
# 傳入匯編機器碼得到機器碼列表
def GetOpCode(dbg, Code):
ShellCode = []
for index in Code:
ref = get_opcode_from_assemble(dbg,index)
for opcode in ref:
ShellCode.append(opcode)
return ShellCode
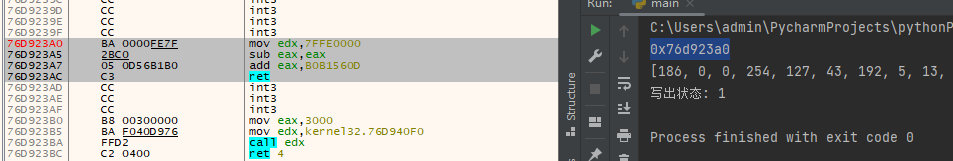
def Patch_GetTickCount(dbg):
# 得到模塊句柄
ispresent = dbg.get_module_from_function("kernel32.dll","GetTickCount")
print(hex(ispresent))
# 將反調試語句轉為機器碼
ShellCode = GetOpCode(dbg,
[
"mov edx,0x7ffe0000",
"sub eax,eax",
"add eax,0xB0B1560D",
"ret"
]
)
print(ShellCode)
flag = 0
for index in range(0,len(ShellCode)):
flag = dbg.write_memory_byte(ispresent + index,ShellCode[index])
if flag:
flag = 1
else:
flag = 0
return flag
if __name__ == "__main__":
dbg = MyDebug()
connect = dbg.connect()
ref = Patch_GetTickCount(dbg)
print("寫出狀態: {}".format(ref))
dbg.close()寫出效果如下:
此函數打補丁需要跳轉兩次,原因是因為函數開頭部分無法填充更多指令,需要我們自己來申請空間,并實現跳轉。
# ----------------------------------------------
# By: LyShark
# Email: me@lyshark.com
# Project: https://github.com/lyshark/LyScript
# ----------------------------------------------
from LyScript32 import MyDebug
# 傳入匯編代碼,得到對應機器碼
def get_opcode_from_assemble(dbg_ptr,asm):
byte_code = bytearray()
addr = dbg_ptr.create_alloc(1024)
if addr != 0:
asm_size = dbg_ptr.assemble_code_size(asm)
# print("匯編代碼占用字節: {}".format(asm_size))
write = dbg_ptr.assemble_write_memory(addr,asm)
if write == True:
for index in range(0,asm_size):
read = dbg_ptr.read_memory_byte(addr + index)
# print("{:02x} ".format(read),end="")
byte_code.append(read)
dbg_ptr.delete_alloc(addr)
return byte_code
else:
return bytearray(0)
# 傳入匯編機器碼得到機器碼列表
def GetOpCode(dbg, Code):
ShellCode = []
for index in Code:
ref = get_opcode_from_assemble(dbg,index)
for opcode in ref:
ShellCode.append(opcode)
return ShellCode
# 獲取指定位置前index條指令的長度
def GetOpCodeSize(dbg,address,index):
ref_size = 0
dasm = dbg.get_disasm_code(address,index)
for index in dasm:
count = dbg.assemble_code_size(index.get("opcode"))
ref_size += count
return ref_size
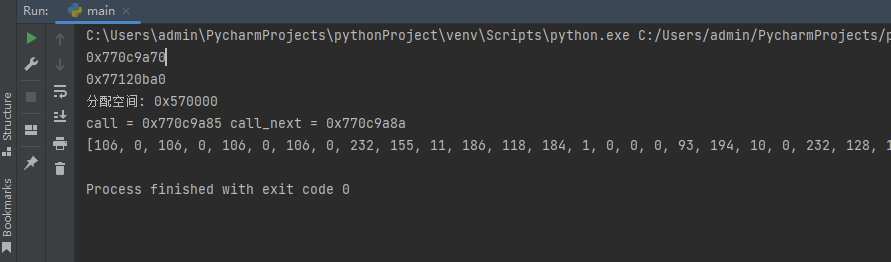
def Patch_ZwQueryInformationProcess(dbg):
# 得到模塊句柄
ispresent = dbg.get_module_from_function("ntdll.dll","ZwQueryInformationProcess")
print(hex(ispresent))
create_address = dbg.create_alloc(1024)
print("分配空間: {}".format(hex(create_address)))
# 將反調試語句轉為機器碼
ShellCode = GetOpCode(dbg,
[
"cmp dword [esp + 8],7",
"DB 0x74",
"DB 0x06",
f"push {hex(ispresent)}",
"ret",
"mov eax,dword [esp +0x0c]",
"push 0",
"pop dword [eax]",
"xor eax,eax",
"ret 14"
]
)
print(ShellCode)
# 把shellcode寫出到自己分配的堆中
flag = 0
for index in range(0,len(ShellCode)):
flag = dbg.write_memory_byte(create_address + index,ShellCode[index])
if flag:
flag = 1
else:
flag = 0
# 填充跳轉位置
jmp_shellcode = GetOpCode(dbg,
[
f"push {hex(create_address)}",
"ret"
]
)
for index in range(0,len(jmp_shellcode)):
flag = dbg.write_memory_byte(ispresent + index,jmp_shellcode[index])
if flag:
flag = 1
else:
flag = 0
return flag
if __name__ == "__main__":
dbg = MyDebug()
connect = dbg.connect()
ref = Patch_ZwQueryInformationProcess(dbg)
print("補丁狀態: {}".format(ref))
dbg.close()這段代碼運行后,首先會申請內存,然后將特定的一段機器碼寫出到此內存中。
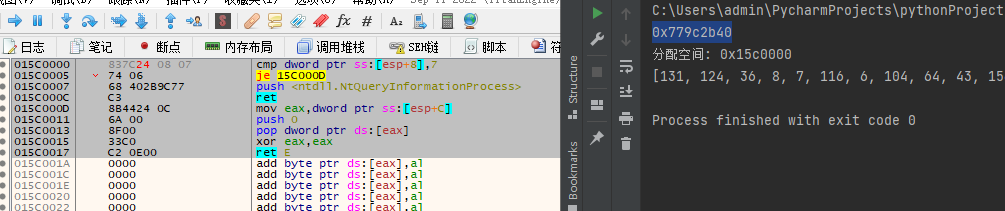
內存寫出以后,再將函數頭部替換為跳轉,這樣一來當函數被調用,也就自動轉向了。
FindWindow函數功能是取窗體句柄,有AW與Ex系列,使用同上方法替代即可。
# ----------------------------------------------
# By: LyShark
# Email: me@lyshark.com
# Project: https://github.com/lyshark/LyScript
# ----------------------------------------------
from LyScript32 import MyDebug
import ctypes
# 傳入匯編代碼,得到對應機器碼
def get_opcode_from_assemble(dbg_ptr,asm):
byte_code = bytearray()
addr = dbg_ptr.create_alloc(1024)
if addr != 0:
asm_size = dbg_ptr.assemble_code_size(asm)
# print("匯編代碼占用字節: {}".format(asm_size))
write = dbg_ptr.assemble_write_memory(addr,asm)
if write == True:
for index in range(0,asm_size):
read = dbg_ptr.read_memory_byte(addr + index)
# print("{:02x} ".format(read),end="")
byte_code.append(read)
dbg_ptr.delete_alloc(addr)
return byte_code
else:
return bytearray(0)
# 傳入匯編機器碼得到機器碼列表
def GetOpCode(dbg, Code):
ShellCode = []
for index in Code:
ref = get_opcode_from_assemble(dbg,index)
for opcode in ref:
ShellCode.append(opcode)
return ShellCode
def Patch_FindWindow(dbg):
# 得到模塊句柄
FindWindowA = dbg.get_module_from_function("user32.dll","FindWindowA")
FindWindowW = dbg.get_module_from_function("user32.dll","FindWindowW")
FindWindowExA = dbg.get_module_from_function("user32.dll","FindWindowExA")
FindWindowExW = dbg.get_module_from_function("user32.dll","FindWindowExW")
print("A = {} w = {} exA = {} exW = {}".format(hex(FindWindowA),hex(FindWindowW),hex(FindWindowExA),hex(FindWindowExW)))
# 將反調試語句轉為機器碼
ShellCode = GetOpCode(dbg,
[
"xor eax,eax",
"ret 0x8",
]
)
ShellCodeEx = GetOpCode(dbg,
[
"xor eax,eax",
"ret 0x10",
]
)
# 寫出
flag = 0
for index in range(0,len(ShellCode)):
flag = dbg.write_memory_byte(FindWindowA + index,ShellCode[index])
flag = dbg.write_memory_byte(FindWindowW + index,ShellCode[index])
if flag:
flag = 1
else:
flag = 0
for index in range(0,len(ShellCodeEx)):
flag = dbg.write_memory_byte(FindWindowExA + index,ShellCodeEx[index])
flag = dbg.write_memory_byte(FindWindowExW + index,ShellCodeEx[index])
if flag:
flag = 1
else:
flag = 0
return flag
if __name__ == "__main__":
dbg = MyDebug()
connect = dbg.connect()
ref = Patch_FindWindow(dbg)
print("補丁狀態: {}".format(ref))
dbg.close()補丁應用會分別替換四個函數。
枚舉窗體的補丁與上方代碼一致,此處就不再分析了。
如下案例,實現了在枚舉窗體過程中實現彈窗,并不影響窗體的枚舉。
from LyScript32 import MyDebug
# 傳入匯編代碼,得到對應機器碼
def get_opcode_from_assemble(dbg_ptr,asm):
byte_code = bytearray()
addr = dbg_ptr.create_alloc(1024)
if addr != 0:
asm_size = dbg_ptr.assemble_code_size(asm)
# print("匯編代碼占用字節: {}".format(asm_size))
write = dbg_ptr.assemble_write_memory(addr,asm)
if write == True:
for index in range(0,asm_size):
read = dbg_ptr.read_memory_byte(addr + index)
# print("{:02x} ".format(read),end="")
byte_code.append(read)
dbg_ptr.delete_alloc(addr)
return byte_code
else:
return bytearray(0)
# 傳入匯編機器碼得到機器碼列表
def GetOpCode(dbg, Code):
ShellCode = []
for index in Code:
ref = get_opcode_from_assemble(dbg,index)
for opcode in ref:
ShellCode.append(opcode)
return ShellCode
# 獲取指定位置前index條指令的長度
def GetOpCodeSize(dbg,address,index):
ref_size = 0
dasm = dbg.get_disasm_code(address,index)
for index in dasm:
count = dbg.assemble_code_size(index.get("opcode"))
ref_size += count
return ref_size
def Patch_EnumWindows(dbg):
# 得到模塊句柄
address = dbg.get_module_from_function("user32.dll","EnumWindows")
print(hex(address))
msg_box = dbg.get_module_from_function("user32.dll","MessageBoxA")
print(hex(msg_box))
create_address = dbg.create_alloc(1024)
print("分配空間: {}".format(hex(create_address)))
# 找call地址,找到后取出他的內存地址
dasm_list = dbg.get_disasm_code(address,20)
call_addr = 0
call_next_addr = 0
for index in range(0,len(dasm_list)):
# 如果找到了call,取出call地址以及下一條地址
if dasm_list[index].get("opcode").split(" ")[0] == "call":
call_addr = dasm_list[index].get("addr")
call_next_addr = dasm_list[index+1].get("addr")
print("call = {} call_next = {}".format(hex(call_addr),hex(call_next_addr)))
# 將反調試語句轉為機器碼
ShellCode = GetOpCode(dbg,
[
"push 0",
"push 0",
"push 0",
"push 0",
f"call {hex(msg_box)}",
"mov eax,1",
"pop ebp",
"ret 10",
f"call {hex(call_addr)}",
"pop ebp",
"ret 8"
]
)
print(ShellCode)
# 把shellcode寫出到自己分配的堆中
flag = 0
for index in range(0,len(ShellCode)):
flag = dbg.write_memory_byte(create_address + index,ShellCode[index])
if flag:
flag = 1
else:
flag = 0
# 填充跳轉位置
jmp_shellcode = GetOpCode(dbg,
[
f"push {hex(create_address)}",
"ret"
]
)
for index in range(0,len(jmp_shellcode)):
flag = dbg.write_memory_byte(call_addr + index,jmp_shellcode[index])
if flag:
flag = 1
else:
flag = 0
return flag
if __name__ == "__main__":
dbg = MyDebug()
connect = dbg.connect()
ref = Patch_EnumWindows(dbg)
dbg.close()輸出效果如下:
到此,相信大家對“LyScript怎么實現Hook隱藏調試器”有了更深的了解,不妨來實際操作一番吧!這里是億速云網站,更多相關內容可以進入相關頻道進行查詢,關注我們,繼續學習!
免責聲明:本站發布的內容(圖片、視頻和文字)以原創、轉載和分享為主,文章觀點不代表本網站立場,如果涉及侵權請聯系站長郵箱:is@yisu.com進行舉報,并提供相關證據,一經查實,將立刻刪除涉嫌侵權內容。