溫馨提示×
您好,登錄后才能下訂單哦!
點擊 登錄注冊 即表示同意《億速云用戶服務條款》
您好,登錄后才能下訂單哦!
1.公司內網用戶需要通過網關服務器共享上網
2.互聯網用戶需要訪問網站服務器
3.只允許192.168.1 .0/24ping網關和服務器
4.網站服務器和網關服務器均通過SSH來遠程管理,為了安全,將SSH默認端口改為12345,只允許192.168.1.10主機SSH網關和服務器,允許互聯網SSH內部服務器
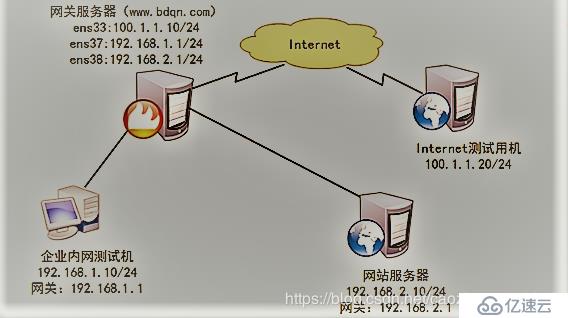 1.網關服務器:Centos7 -1
1.網關服務器:Centos7 -1
2.企業內網測試機:Centos7 -2
3.網站服務器:Centos7 -3
4.Internet測試機:Centos7 -4
1.添加網卡,并綁定網卡為VMent2僅主機模式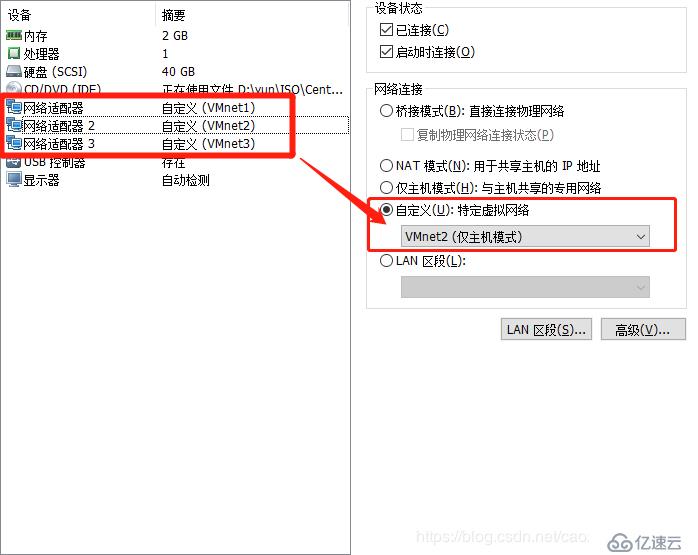
2.配置并確認網關地址
[root@192 network-scripts]# ifconfig
ens33: flags=4163<UP,BROADCAST,RUNNING,MULTICAST> mtu 1500
inet 100.1.1.10 netmask 255.255.255.0 broadcast 100.1.1.255
inet6 fe80::839c:1220:87fc:aef prefixlen 64 scopeid 0x20<link>
ether 00:0c:29:70:78:f5 txqueuelen 1000 (Ethernet)
RX packets 2715 bytes 723845 (706.8 KiB)
RX errors 0 dropped 0 overruns 0 frame 0
TX packets 623 bytes 55679 (54.3 KiB)
TX errors 0 dropped 0 overruns 0 carrier 0 collisions 0
ens36: flags=4163<UP,BROADCAST,RUNNING,MULTICAST> mtu 1500
inet 192.168.10.1 netmask 255.255.255.0 broadcast 192.168.1.255
inet6 fe80::3d7f:4cdc:f7ec:8638 prefixlen 64 scopeid 0x20<link>
ether 00:0c:29:70:78:09 txqueuelen 1000 (Ethernet)
RX packets 38 bytes 7923 (7.7 KiB)
RX errors 0 dropped 0 overruns 0 frame 0
TX packets 143 bytes 24516 (23.9 KiB)
TX errors 0 dropped 0 overruns 0 carrier 0 collisions 0
ens37: flags=4163<UP,BROADCAST,RUNNING,MULTICAST> mtu 1500
inet 192.168.20.1 netmask 255.255.255.0 broadcast 192.168.2.255
inet6 fe80::a6c3:1677:f71d:8e29 prefixlen 64 scopeid 0x20<link>
ether 00:0c:29:70:78:ff txqueuelen 1000 (Ethernet)
RX packets 38 bytes 7923 (7.7 KiB)
RX errors 0 dropped 0 overruns 0 frame 0
TX packets 138 bytes 23100 (22.5 KiB)
TX errors 0 dropped 0 overruns 0 carrier 0 collisions 03.開啟路由轉發功能
[root@192 network-scripts]# vim /etc/sysctl.conf
...... //省略注釋內容
net.ipv4.ip_forward = 1 //添加此條目
[root@192 network-scripts]# sysctl -p //載入sysctl配置文件
net.ipv4.ip_forward = 11.綁定網卡為VMent3僅主機模式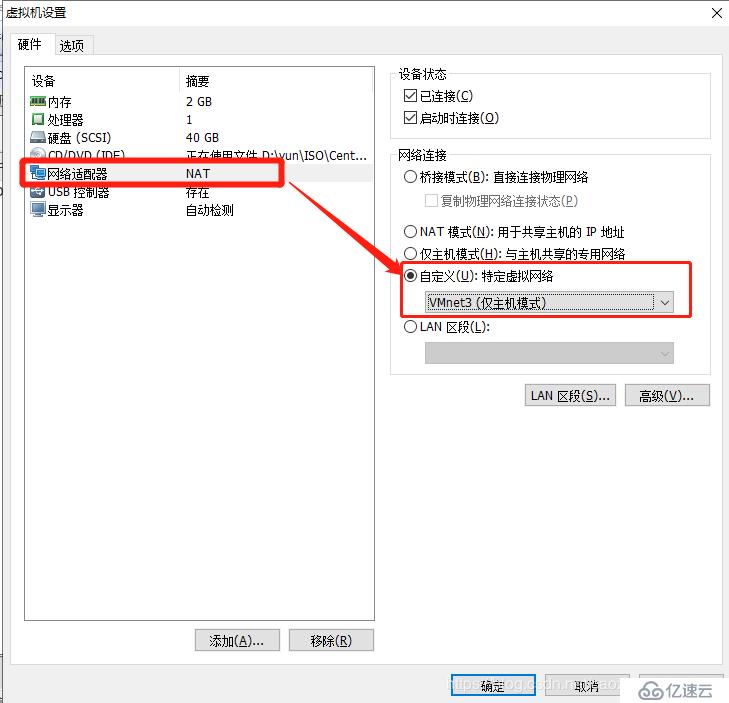
2.配置并確認IP地址與網關
[root@192 network-scripts]# ifconfig //查看ip地址及子網掩碼
ens33: flags=4163<UP,BROADCAST,RUNNING,MULTICAST> mtu 1500
inet 192.168.10.10 netmask 255.255.255.0 broadcast 192.168.1.255
inet6 fe80::839c:1220:87fc:aef prefixlen 64 scopeid 0x20<link>
ether 00:0c:29:90:44:7f txqueuelen 1000 (Ethernet)
RX packets 2647 bytes 190172 (185.7 KiB)
RX errors 0 dropped 0 overruns 0 frame 0
TX packets 453 bytes 51940 (50.7 KiB)
TX errors 0 dropped 0 overruns 0 carrier 0 collisions 0
[root@192 network-scripts]# route -n //查看路由信息
Kernel IP routing table
Destination Gateway Genmask Flags Metric Ref Use Iface
192.168.10.0 0.0.0.0 255.255.255.0 U 100 0 0 ens33
1.先在聯網狀態下載安裝httpd服務
[root@192 ~]# yum install httpd -y2.綁定網卡為VMent3僅主機模式**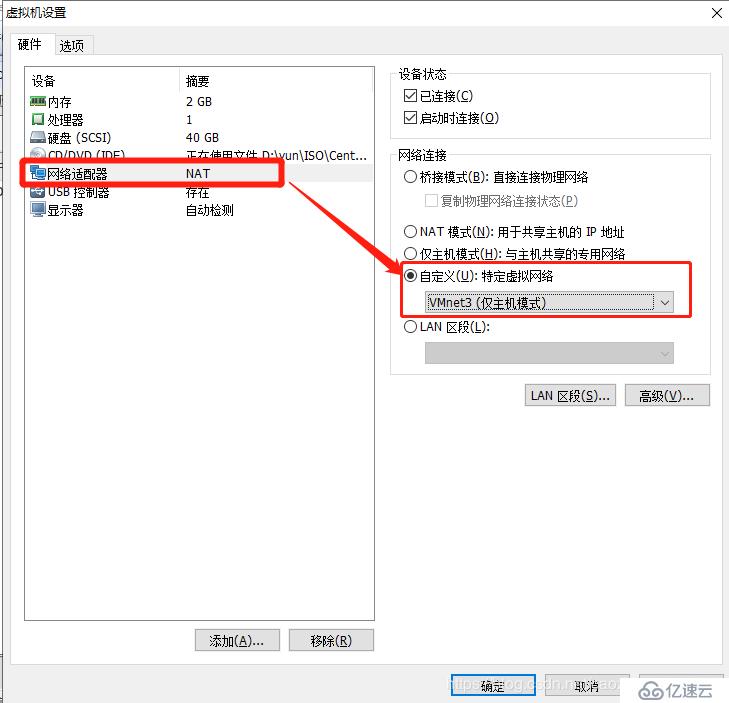
3.配置并確認IP地址與網關
[root@dmz ~]# ifconfig
ens33: flags=4163<UP,BROADCAST,RUNNING,MULTICAST> mtu 1500
inet 192.168.20.20 netmask 255.255.255.0 broadcast 192.168.2.255
inet6 fe80::839c:1220:87fc:aef prefixlen 64 scopeid 0x20<link>
inet6 fe80::791b:db71:8a12:f34 prefixlen 64 scopeid 0x20<link>
ether 00:0c:29:de:4a:b8 txqueuelen 1000 (Ethernet)
RX packets 5353 bytes 3513622 (3.3 MiB)
RX errors 0 dropped 0 overruns 0 frame 0
TX packets 1143 bytes 105439 (102.9 KiB)
TX errors 0 dropped 0 overruns 0 carrier 0 collisions 0
[root@dmz ~]# route -n
Kernel IP routing table
Destination Gateway Genmask Flags Metric Ref Use Iface
192.168.20.0 0.0.0.0 255.255.255.0 U 100 0 0 ens334.開啟網站服務
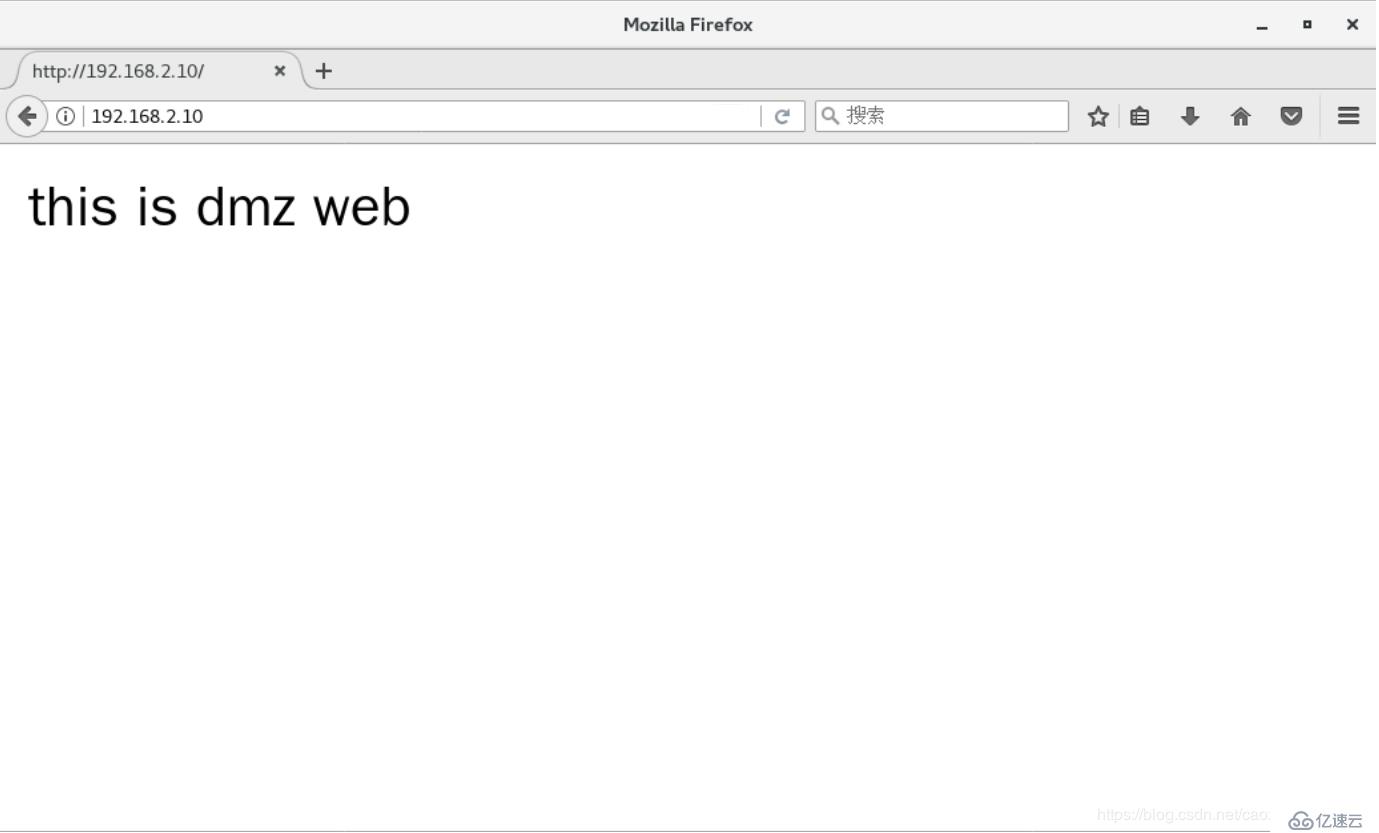
[root@192 ~]# vim /var/www/html/index.html
[root@192 ~]# cat /var/www/html/index.html
<h2>this is dmz web</h2>
[root@dmz html]# systemctl start httpdsuccess
[root@dmz ~]# firewall-cmd --add-service=http --zone=dmz --permanent //將防火墻的默認區域改為dmz區域
success
[root@dmz ~]# firewall-cmd --remove-service=ssh --zone=dmz --permanent //添加http服務到dmz區域永久設置中
success
[root@dmz ~]# firewall-cmd --add-icmp-block=echo-request --zone=dmz --permanent //禁止使用ssh進行登錄
success
[root@dmz ~]# firewall-cmd --reload //重載防火墻
success1.先在聯網狀態下載安裝httpd服務
[root@192 ~]# yum install httpd -y2.綁定網卡為VMent1僅主機模式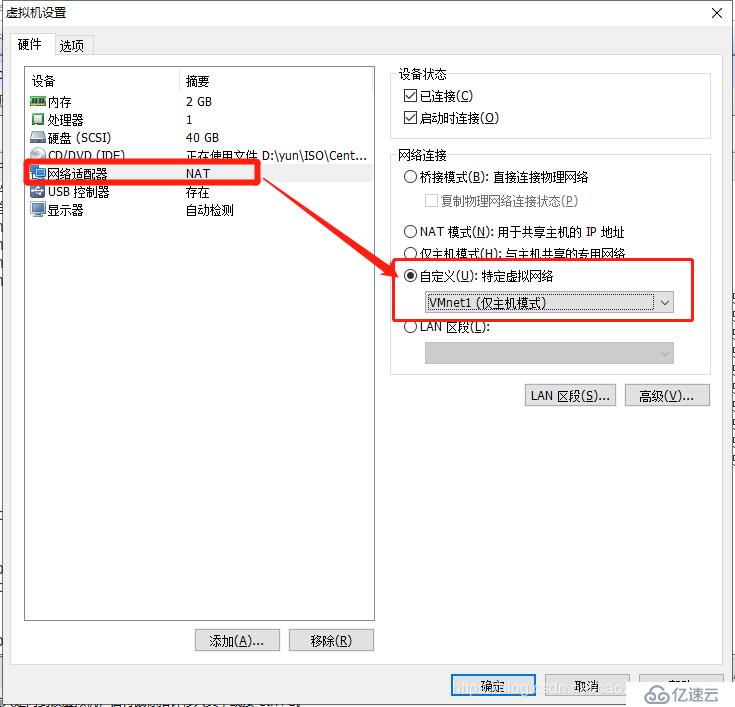
3.配置并確認IP地址與網關
[root@192 ~]# ifconfig
ens33: flags=4163<UP,BROADCAST,RUNNING,MULTICAST> mtu 1500
inet 100.1.1.20 netmask 255.255.255.0 broadcast 100.1.1.255
inet6 fe80::839c:1220:87fc:aef prefixlen 64 scopeid 0x20<link>
inet6 fe80::791b:db71:8a12:f34 prefixlen 64 scopeid 0x20<link>
ether 00:0c:29:9e:f9:aa txqueuelen 1000 (Ethernet)
RX packets 6587 bytes 4090863 (3.9 MiB)
RX errors 0 dropped 0 overruns 0 frame 0
TX packets 1266 bytes 105686 (103.2 KiB)
TX errors 0 dropped 0 overruns 0 carrier 0 collisions 0
[root@192 ~]# route -n
Kernel IP routing table
Destination Gateway Genmask Flags Metric Ref Use Iface
100.1.1.0 0.0.0.0 255.255.255.0 U 100 0 0 ens334.開啟網站服務,并關閉防火墻與增強型安全功能
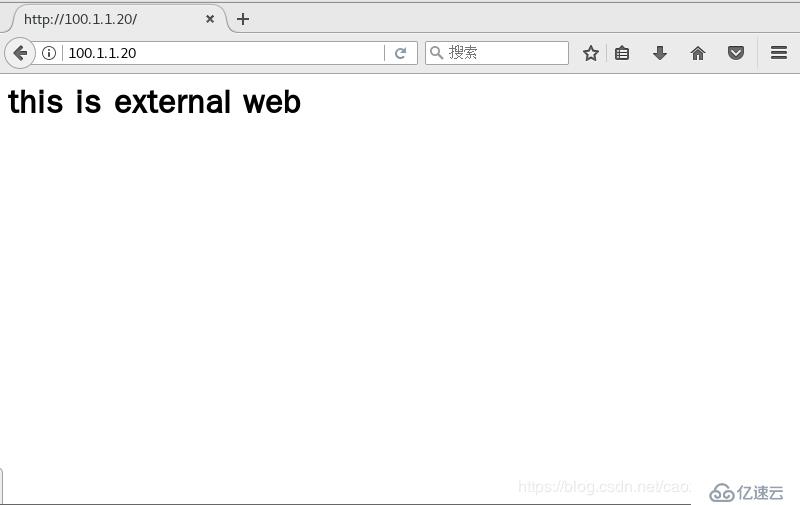
[root@192 ~]# vim /var/www/html/index.html
[root@192 ~]# cat /var/www/html/index.html
<h2>this is external web</h2>
[root@192 ~]# systemctl stop firewalld.service
[root@192 ~]# setenforce 0 [root@192 ~]# firewall-cmd --set-default-zone=external //將防火墻默認區域改為extemal
success
[root@192 ~]# firewall-cmd --change-interface=ens36 --zone=trusted --permanent //將ens36網卡設為信任區域
The interface is under control of NetworkManager, setting zone to 'trusted'.
success
[root@192 ~]# firewall-cmd --change-interface=ens37 --zone=dmz --permanent //將ens37網卡設為dmz區域
The interface is under control of NetworkManager, setting zone to 'dmz'.
success
[root@192 ~]# firewall-cmd --zone=dmz --remove-service=ssh --permanent //dmz區域內禁止使用ssh登錄
success
[root@192 ~]# firewall-cmd --zone=dmz --add-service=http --permanent //dmz區域內添加http服務
success
[root@192 ~]# firewall-cmd --zone=dmz --add-icmp-block=echo-request --permanent //dmz區域內阻塞icmp協議
success
[root@192 ~]# firewall-cmd --zone=external --add-service=http --permanent //在外部區域添加http服務
success
[root@192 ~]# firewall-cmd --reload //重載防火墻
success
[root@192 ~]# firewall-cmd --zone=external --add-forward port=port=80:proto=tcp:toaddr=192.168.2.10 --permanent //設定端口映射
success
[root@192 ~]# firewall-cmd --reload //重載防火墻
success
免責聲明:本站發布的內容(圖片、視頻和文字)以原創、轉載和分享為主,文章觀點不代表本網站立場,如果涉及侵權請聯系站長郵箱:is@yisu.com進行舉報,并提供相關證據,一經查實,將立刻刪除涉嫌侵權內容。